How Attackers Can Own a Business Without Touching the Endpoint
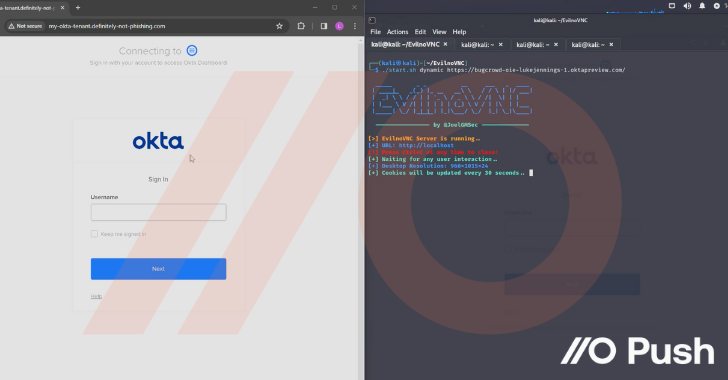
Attackers are increasingly making use of “networkless” attack techniques targeting cloud apps and identities. Here’s how attackers can (and are) compromising organizations – without ever needing to touch the endpoint or conventional networked systems and services.
Before getting into the details of the attack techniques being used, let’s discuss why
2024-04-19 11:08:00
News
Ukrainian REvil Hacker Sentenced to 13 Years and Ordered to Pay $16 Million
Ukrainian REvil Hacker Sentenced to 13 Years and Ordered to Pay $16 Million A Ukrainian national has been sentenced to more than 13 years in prison and ordered to pay $16 million in restitution for Read more…



0 Comments